Shared Responsibility in Cloud
Summary
This note explains the shared responsibility model in cloud environments. The goal is to understand that using AWS or Azure does not remove the need for security, operations, and verification on the customer side.
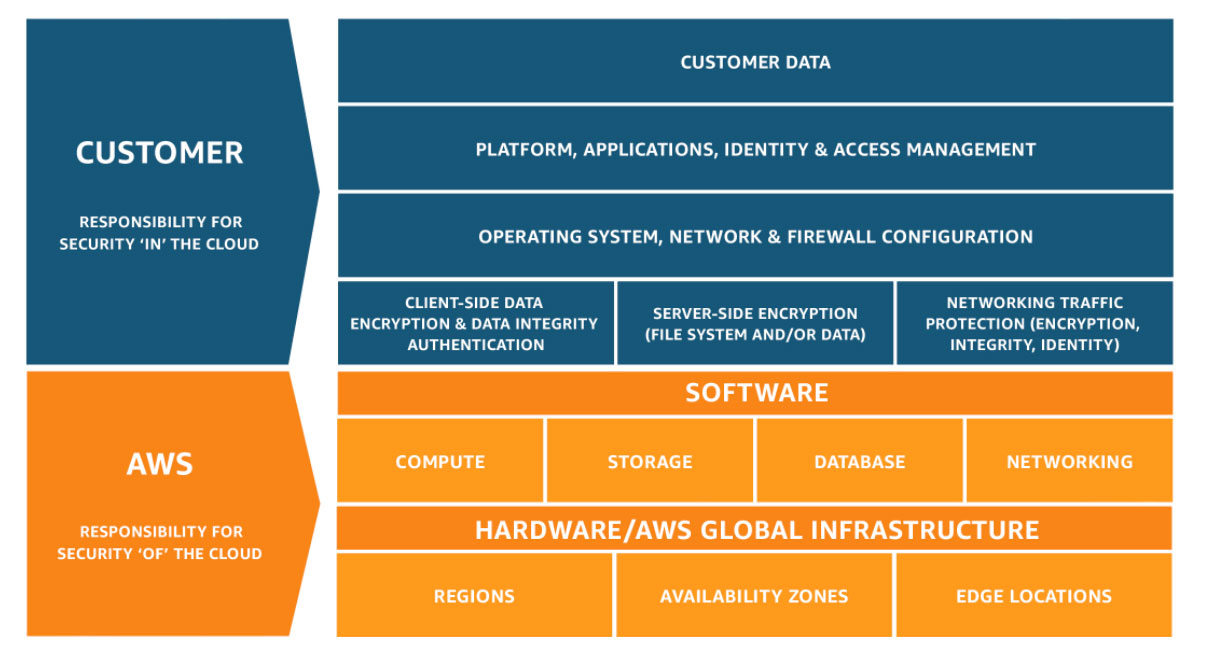
Official AWS diagram showing how the boundary shifts between provider and customer responsibility.
Why this matters
- many beginner cloud mistakes come from assuming the provider handles more than it actually does
- security, logging, IAM, and configuration still require customer decisions
- this model helps explain why cloud operations are different from simply “renting servers”
Environment / Scope
| Item | Value |
|---|---|
| Topic | shared responsibility model |
| Best use for this note | building cloud operations awareness |
| Main focus | provider responsibility vs customer responsibility |
| Safe to practise? | yes |
Key concepts
- Provider responsibility - what the cloud platform secures and operates on its own side
- Customer responsibility - what you still need to configure, secure, and monitor
- Operational visibility - the evidence you use to confirm that your side is healthy and secure
Mental model
Think about the model like this:
cloud provider runs the platform
customer configures and uses the services safelyThe exact line changes by service type, but the customer is never fully removed from responsibility.
Everyday examples
| Example | What still belongs to you |
|---|---|
| deploy a serverless function | IAM, logging, config, secrets, monitoring |
| create cloud storage | access control, data handling, lifecycle choices |
| build a VM or instance | OS hardening, patching, access, monitoring |
| use a managed identity or app service | role scope, logging, safe usage |
Common misunderstandings
| Misunderstanding | Better explanation |
|---|---|
| ”Cloud provider secures everything for me” | the provider secures the platform, not every customer decision |
| ”Managed service means no operational work” | logging, monitoring, IAM, and validation still matter |
| ”If it deployed successfully, it is secure enough” | successful deployment and good security are different things |
| ”Cloud removes the need for troubleshooting” | troubleshooting still exists, just with different layers and tools |
Verification
| Check | Expected result |
|---|---|
| Service boundary is understood | you can explain what the provider handles vs what you handle |
| IAM and logging are considered | operational responsibilities are visible |
| Configuration choices are deliberate | not left to assumption |
| Risk awareness improves | cloud decisions feel less magical |
Pitfalls / Troubleshooting
| Problem | Likely cause | What to check |
|---|---|---|
| Cloud issue feels vague | unclear ownership boundary | provider vs customer responsibility |
| Access is too broad | weak IAM thinking | roles and permissions |
| Service works but is hard to observe | logging and monitoring were skipped | operational visibility |
| Deployment is fast but fragile | config and responsibility model were not thought through | assumptions made during setup |
Key takeaways
- cloud still requires customer-side security and operational thinking
- managed services reduce some work, but not all responsibility
- the shared responsibility model is one of the best foundations for cloud troubleshooting and design